Hackers Pick Up Clues From Google’s Internet Indexing
In 2013, the Westmore News, a modest newspaper serving the suburban neighborhood of Rye Brook, New York, ran a aspect on the opening of a sluice gate at the Bowman Avenue Dam. Costing some $2 million, the new gate, then nearing completion, was built to reduce flooding downstream.
The function caught the eye of a range of local politicians, who collected to shake fingers at the official unveiling. “I’ve been to loads of ribbon-cuttings,” county government Rob Astorino was quoted as saying. “This is my to start with sluice gate.”
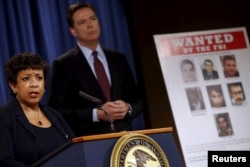
But locals evidently were not the only types with their eyes on the dam’s new sluice. According to an indictment handed down late final 7 days by the U.S. Section of Justice, Hamid Firoozi, a very well-recognized hacker primarily based in Iran, gained obtain many occasions in 2013 to the dam’s manage programs. Experienced the sluice been completely operational and connected to those people systems, Firoozi could have produced major injury. Fortuitously for Rye Brook, it was not.
Hack attacks probing crucial U.S. infrastructure are almost nothing new. What alarmed cybersecurity analysts in this scenario, on the other hand, was Firoozi’s apparent use of an outdated trick that pc nerds have quietly recognized about for many years.
It is referred to as “dorking” a look for engine — as in “Google dorking” or “Bing dorking” — a tactic extensive utilized by cybersecurity specialists who get the job done to close safety vulnerabilities.
Now, it appears, the hackers know about it as properly.
Hiding in open watch
“What some contact dorking we truly contact open up-supply network intelligence,” reported Srinivas Mukkamala, co-founder and CEO of the cyber-hazard evaluation agency RiskSense. “It all depends on what you question Google to do.”
Mukkamala claims that search engines are consistently trolling the World-wide-web, hunting to record and index every device, port and unique IP tackle related to the Web. Some of these factors are created to be general public — a restaurant’s homepage, for instance — but several other individuals are intended to be private — say, the protection camera in the restaurant’s kitchen. The problem, says Mukkamala, is that as well a lot of individuals do not realize the change prior to heading online.
“There is the Net, which is everything that’s publicly addressable, and then there are intranets, which are meant to be only for interior networking,” he explained to VOA. “The look for engines never care which is which they just index. So if your intranet isn’t configured thoroughly, that’s when you get started viewing details leakage.”
Though a restaurant’s shut-circuit camera might not pose any actual stability danger, several other items having related to the Net do. These contain stress and temperature sensors at power vegetation, SCADA devices that handle refineries, and operational networks — or OTs — that retain key production plants doing the job.
Irrespective of whether engineers know it or not, a lot of of these matters are currently being indexed by research engines, leaving them quietly hiding in open up watch. The trick of dorking, then, is to figure out just how to locate all all those belongings indexed on-line.
As it turns out, it is really genuinely not that really hard.
An asymmetric risk
“The matter with dorking is you can publish personalized searches just to seem for that information [you want],” he stated. “You can have many nested look for conditions, so you can go granular, permitting you to obtain not just just about every solitary asset, but every other asset which is connected to it. You can really dig deep if you want,” stated RiskSense’s Mukkamala.
Most key look for engines like Google offer sophisticated lookup capabilities: commands like “filetype” to hunt for precise kinds of data files, “numrange” to find particular digits, and “intitle,” which seems for exact website page textual content. What’s more, different lookup parameters can be nested one particular in one more, creating a pretty fine electronic web to scoop up data.
For example, in its place of just coming into “Brook Avenue Dam” into a lookup motor, a dorker may well use the “inurl” perform to hunt for webcams on the web, or “filetype” to appear for command and control files and features. Like a scavenger hunt, dorking entails a specified sum of luck and endurance. But skillfully employed, it can greatly improve the chance of acquiring something that should not be general public.
Like most factors on the internet, dorking can have good employs as perfectly as destructive. Cybersecurity gurus ever more use these types of open-resource indexing to find vulnerabilities and patch them prior to hackers stumble upon them.
Dorking is also very little new. In 2002, Mukkamala suggests, he labored on a challenge checking out its probable hazards. A lot more not too long ago, the FBI issued a general public warning in 2014 about dorking, with assistance about how community directors could defend their techniques.
The difficulty, states Mukkamala, is that pretty much everything that can be linked is currently being hooked up to the World-wide-web, frequently with out regard for its safety, or the security of the other objects it, in change, is connected to.
“All you have to have is a single vulnerability to compromise the method,” he told VOA. “This is an asymmetric, popular menace. They [hackers] really don’t require something else than a notebook and connectivity, and they can use the resources that are there to start launching assaults.
“I you should not consider we have the knowledge or resources to protect in opposition to this risk, and we’re not geared up.”
That, Mukkamala warns, usually means it’s far more most likely than not that we’ll see extra cases like the hacker’s exploit of the Bowman Avenue Dam in the yrs to appear. Regrettably, we may possibly not be as lucky the following time.